Published on Wednesday, 28 Jun, 2017
Transformations don't need to be about technology
A recent project first started with a simple premise: what tools can we build to better support people? After undertaking several discovery activities, it turned out that the solution was much less complicated, and much more human-led.
Many typical projects often involve an expert review of a website as part of the initial discovery process, but in this instance there were a few more in the mix - over 200! The collection of websites that this investigation centered around were all community websites created and controlled by entirely different volunteers, using hugely varying technologies and approaches, but each was aligned in terms of purpose and relationship to the others. This network of sites was functioning entirely self-sufficiently, but after a security scare on one it was decided by my client (a related and supporting party) that a general review should be undertaken, with a view to better understanding what we could do to improve this area. This turned into an opportunity to look more strategically at the bigger picture and make some recommendations. Could we create some tools to help people build better websites?
Information gathering
The initial idea was that all of the disparate sites could be provided with some uniformity in order to help them to be the best that they could. For instance, to support the sites it could have been possible to do things like:
- Build further features into pages of an existing website, and provide access to the community
- Build a platform which supports limited customisation of pre-defined templates
- Build a platform which supports more flexible customisation
- Provide assets for people to use to create their own sites
But before that, the starting point was to lay out all of the pieces of the puzzle. We realised that we didn’t even have a complete and up-to-date picture of the URLs for all of the existing sites, or a view of who was using third party social platforms like Facebook rather than creating websites themselves. The first step was to create a humble spreadsheet of all of the entities, and work to match them with their digital presences.
After tracking them all down, the next step was born out of the security scare – we wanted to know the technology that each was using. This element used a combination of manual and automated checks; some certainties and some good guesses. Our findings here confirmed the level of fragmentation of approaches, with websites being generated by obsolete software, modern software, being coded by hand, using both proprietary and open source content management systems, hosted platforms, and site builders. Both general and specific security advice were drafted, ready to be shared with the maintainers.
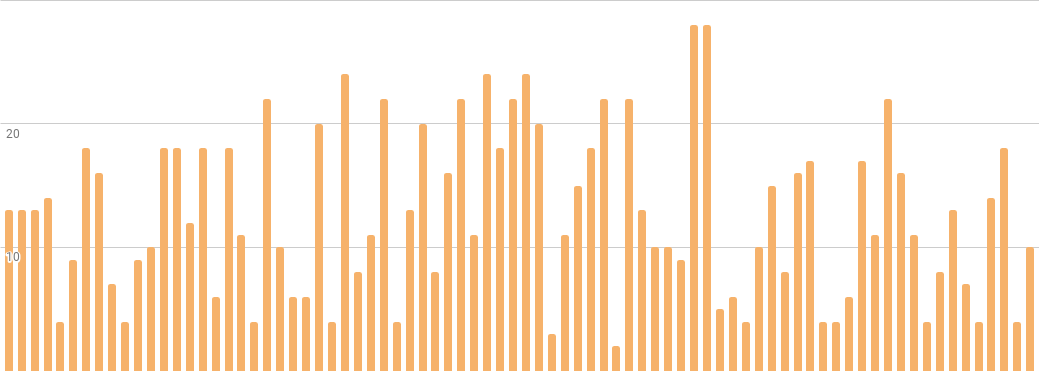
Next came a more in-depth check — how did the sites fare when held up against certain criteria? Were they still working? Was there any evidence of security breaches? What was the design and usability like? How about the technology? Was it being used and updated, and how future-proof was it judged to be? With scoring applied, an overall picture began to emerge of the spread of where these 200-odd sites sat on the scale.
But what of the content itself? Further questions came to mind, as many sites followed similar patterns. Were they looking to others and copying them, or did the similarities in content and structure stem from independent origins?
With these and other questions mounting, there was only one thing for it - let’s speak to some people and ask them!
Interviews with maintainers
Aided by a colleague, we attempted to contact the maintainers of websites using the contact details made public. Our goal was to speak to a range of people whose sites sat across the spectrum, or where our initial review had turned up some interesting points that we wanted to explore more.
These contact efforts in themselves were telling, with a large number of people not getting back to us, or not having the time to be able to chat. Many of the issues seen on the sites could be traced back to them being slowly abandoned, or created by people who didn’t always have time to manage them.
For those able to speak to us, we were able to discuss several key areas including a bit about their situation, the process they went through to create and update sites, any issues they’ve faced, and crucially “is there anything we could do to better support you?".
The answer to this was almost unanimously nothing to do with technology.
Technology isn’t always the answer
We set out on this journey with assumptions that some would want tools and others wouldn’t, but that this split would be more about some wanting to keeping autonomy rather than the group as a whole potentially gaining more from other areas of focus. Instead, what we heard was that it was all about better defining communication channels, facilitating more of a community support network, and providing educational resources and advice - things for people to refer to and learn from. Security - the thing that started it all - would likely improve as a by-product of all of these other actions, as hopefully would the overall quality of sites.
“We need enablers, not controllers. Assisting, not telling.”
- Interview participant
Very often, many people decide that the way to fix is technical problem is a systems-led solution, but when we trace back to root causes and take some further time to speak to people and understand what’s really going on, we can get a totally different view of the picture. It’s very easy to waste resources building things that aren’t actually needed, which then struggle to get adopted because they’re not meeting needs, or are overly restrictive. In this instance, immediately creating a reactive, technical solution to assume control of websites after a security breach would not only have been expensive, but would also have gone against people’s wider needs and wants.
So what of the volunteers that we spoke to? The plan is now to keep them as a key audience and specific set of people to consult for future projects - to make sure that we’re thinking about and supporting them from different angles rather than just one. This will start with the recommendations captured as a result of the investigations, but will also go beyond - better thinking about how existing standards can be shared, into requirements for an existing internal project, but also a potential future project that may involve creation of technology and an offer to optionally extend it to this audience. This would however be a pull and not a push - a solution not dictated, but created alongside people, where there are different levels that they’d be able to engage with it. As for the security angle, recommendations and advice have been shared as the first step towards better resources and helping people learn.
The next time you’re faced with a technology problem, rather than jumping to the conclusion that the solution should also be technical, instead try to look more broadly and speak to the people who you’d be affecting. You may well be surprised at what other options become available, and the wider benefits that you could gain.
Read more from the blog
Back in time:
Rebranding and rebuilding
Forward in time:
Trying to write better job descriptions
Posted by Sally Lait
Sally is the lead consultant and founder of Records Sound the Same, helping people with digital transformation. She's also a speaker, coder, gamer, author, and jasmine tea fiend.
 Sally Lait
Sally Lait